'Very high level of confidence' Russia used Kaspersky software for devastating NSA leaks
Three months after U.S. officials asserted that Russian intelligence used popular antivirus company Kaspersky to steal U.S. classified information, there are indications that the alleged espionage is related to a public campaign of highly damaging NSA leaks by a mysterious group called the Shadow Brokers.
“That’s a Russian intelligence operation,” a former senior intelligence official, who requested anonymity to speak bluntly, told Yahoo Finance. “They’ve gotten a lot noisier than they used to be.”

‘A very high level of confidence’
In August 2016, the Shadow Brokers began leaking classified NSA exploit code that amounted to hacking manuals. In October 2017, U.S. officials told major U.S. newspapers that Russian intelligence leveraged software sold by Kaspersky to exfiltrate classified documents from certain computers. (Kaspersky software, like all antivirus software, requires access to everything stored on a computer so that it can scan for malicious software.)
And last week the Wall Street Journal reported that U.S. investigators “now believe that those manuals [leaked by Shadow Brokers] may have been obtained using Kaspersky to scan computers on which they were stored.”
Members of the computer security industry agree with that suspicion.
“I think there’s a very high level of confidence that the Shadow Brokers dump was directly related to Kaspersky … and it’s very much attributable,” David Kennedy, CEO of TrustedSec, told Yahoo Finance. “Unfortunately, we can only hear that from the intelligence side about how they got that information to see if it’s legitimate.”
Dave Aitel, CEO of offensive-minded cybersecurity Immunity, previously explained that there is no “magical way where you can both show the evidence and protect sources and methods.”
After initial reports about the alleged Russian espionage through Kaspersky, the New York Times reported that Israeli officials monitored Russian government hackers as they scanned computers running Kaspersky software to find classified U.S. documents.
Aitel noted that “the Israelis have screenshots and keylogger dumps of this activity happening. To me that says they were watching it in real time. And they know exactly who was at the desk because if they have a keylogger, they know who’s logged in. They know a lot about the people involved, so we haven’t seen all of the information that the Israelis have.”

The public linking by U.S. officials of the alleged espionage-via-Kaspersky to the Shadow Brokers leaks, which the Times described as “one of the worst security debacles ever to befall American intelligence,” would intensify the scandal.
Kennedy reiterated that “the general feeling across the security industry … is that the Shadow Brokers dump was very much so related to information obtained through Kaspersky.”
Kaspersky, which reaches 400 million users worldwide, has repeatedly denied the allegations.
“Unverified opinions about Kaspersky Lab continue to be shared, and should be taken as nothing more than unsubstantiated allegations against a company whose mission has always been to protect against malware regardless of its source, and which has repeatedly extended an offering to help alleviate any substantiated concerns,” Kaspersky Lab stated to Yahoo Finance. “We have never helped and will never help any government with its cyberespionage efforts, and we have no ties with Shadow Brokers or any other cyber-threat actor. We are committed to demonstrating our trustworthiness with our Global Transparency Initiative.”
‘The perfect cyberespionage attack’
The precise sources of the classified material leaked by Shadow Brokers — as well as the specific individuals behind the group — are not clear.
In December, a developer working in the NSA’s elite Tailored Access Operations (TAO) hacking unit pleaded guilty to taking home classified tools that are believed to have been stolen by hackers working for Russian intelligence. The employee, Nghia Hoang Pho, 67, had been using Kaspersky software on his home computer, where he stored the NSA files. Kaspersky said that it had retrieved classified NSA tools through its antivirus software — but claimed to have deleted the information.
In any case, a recent technical analysis by security researcher Patrick Wardle clearly demonstrated how signatures sent by antivirus software like Kaspersky’s could be used to surreptitiously detect and exfiltrate classified documents.
Wardle, chief research officer at Digita Security, told Yahoo Finance that he based the experiment on the question: “Could I create a signature that would seamlessly integrate into [Kaspersky’s] existing antivirus engine that would, instead of looking for malware, look for classified documents?”
The former NSA hacker said that he found “the answer is resoundingly yes, and this is just by nature of what antivirus tools do: They scan for stuff.”
After Wardle explained the process to the New York Times, Kaspersky stated that “it is not possible for Kaspersky Lab products to secretly deliver a specific signature or update to a single user.”
Wardle, who reverse-engineered Kaspersky’s product and tweaked one of the signatures as part of his experiment, doesn’t believe the company’s claim. “It was interesting that Kaspersky didn’t say, ‘We don’t do that.’ They said, ‘It would be impossible to do that,’” Wardle told Yahoo Finance. “[But] they control the update server. You could just filter on IP address, and when that IP address comes in, you could hand it a different set of signatures. So the fact that they said it was impossible to do is very interesting because this is software they control. It’s not impossible — that’s ridiculous.”
In the conclusion of his analysis, Wardle asserted that “a malicious or willing insider within any antivirus company who could tactically deploy such a signature would likely remain undetected.” Furthermore, “any antivirus company that is coerced to, or is willing to, work with a larger entity (such as a government) would equally be able to stealthily leverage their product to detect and exfiltrate any files of interest.”
The circumstances, according to Wardle, makes using antivirus software in this way “the perfect cyberespionage attack.”
Kennedy, citing Wardle’s research, noted that Pho and others like him — NSA employees or contractors running Kaspersky software on home computers containing classified information — would be the targets of this particular Russian espionage operation.
Shadow Brokers leaks ‘like throwing a grenade in the room’
What is striking about the Shadow Brokers leaks is that they became public.
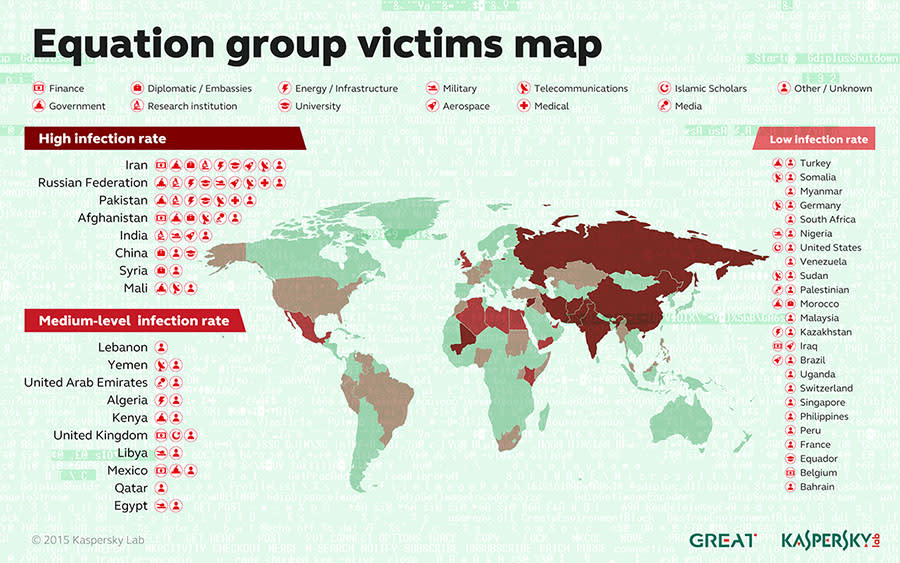
“If you look at what [Russia] burned with the Shadow Brokers dump, those were very good capabilities,” Kennedy said. “You’re talking an exploit that can essentially open any Windows machine that you want to, as well as a number of arsenals around Linux, as well as operations regarding what the U.S. was conducting with the Equation Group. There was a lot of actionable intelligence for Russia,” Kennedy said. “What’s interesting is that they dumped it. And so why did they dump something so valuable?”
The Equation Group, a code name related to the NSA’s TAO hacking, was first publicly detailed by Kaspersky in February 2015. In October 2016, after the Shadow Brokers began leaking NSA tools, the enigmatic group announced that it was holding an auction for Equation Group tools and then canceled the auction.
The latest Shadow Brokers leak of NSA tools occurred in April 2017 and was followed by cyberattacks that leveraged some of the published code. (The CIA reportedly attributed one of those attacks, which primarily targeted Ukraine and erased data from certain computers, to a specialized division of Russia’s GRU military intelligence agency.)
Kennedy, a former U.S. Marines hacker, said that his “purely hypothetical speculation would be that Russia was severely at a disadvantage when it came to our cyber-capabilities and how we were conducting our operations. And they used this method [of stealing U.S. classified tools and leaking them through Shadow Brokers] as a way to weaken and remove a lot of our capabilities to establish some level of dominance again.”
Leaking the Shadow Brokers material, according to the former senior U.S. official who spoke with Yahoo Finance, “is like throwing a grenade in the room. Who cares who you kill? You’re just creating mayhem. You’re disturbing the natural order.”
The former official added: “You throw that stuff out there and our heads are exploding over it. And it serves two purposes: It ties up our resources in trying to address it, to counter it, to shut it down. At the same time, it’s tying up our resources in one place, and what are they doing in another place? What are they doing with the quiet tools? What are they doing while we’re distracted?”

Kennedy noted that the Shadow Brokers situation is just one part of the much larger intelligence game between the U.S. and Russia.
“Why this is so fascinating is that we are now seeing 1/100th of what’s really going on,” Kennedy said. “And that’s what’s unique. This information warfare game that we’re seeing right now is nothing new. We’ve been doing it forever, they’ve been doing it forever — it’s the way that the world works and how we conduct and gain intelligence. … How did we win World War II? Through signals intelligence.”
Kennedy explained that different countries use different techniques and tactics when it comes to modern cyber-operations. The U.S., for example, tends to leverage adversary information by bolstering vulnerable systems or planting false data. Russia, meanwhile, has increasingly exposed U.S. operations in an attempt to neutralize them.
“We have exploit code from Russia. We have capabilities that Russia has used,” Kennedy noted. “The difference is that instead of using [stolen NSA code] for intelligence purposes, Russia used it to destroy our intelligence purposes, which is really one of the first times that we’ve seen that.”
More from Michael B. Kelley:
Expert on Russia’s alleged Kaspersky espionage: The evidence is strong
Russian investigative journalist: Snowden is ‘a sort of ghost’
Why leaked NSA hacking tools are not like stolen Tomahawk missiles
Follow Michael on Twitter @MichaelBKelley.


