Malware study shows people still falling for old tricks, but there’s hope

Too many of us still fall for the old “click this attachment” email trick, and get our computers infected with malware or viruses. The result: our data is increasingly being taken hostage by ransomware creators.
Santa Clara, Calif.-based Malwarebytes’ new “State of Malware Report 2017” brings that and more bad news about security to light. But a chat with one of the people behind the study offered a few reasons to be optimistic, as well. Specifically, that a lot of today’s software, if properly updated, can help protect itself.
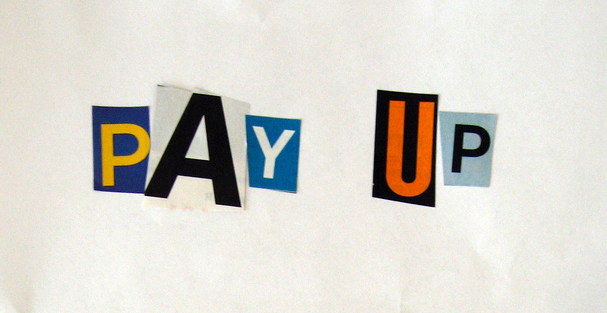
Ransomware rising
Ransomware, or apps that encrypt your data and then demand you pay a ransom (usually in Bitcoin) for a decryption key, have become a big business. In fact, the malware has afflicted everything from hospital computer systems to the occasional “smart” TV to the more than 100 surveillance cameras in Washington hacked days before President Trump’s inauguration.
Malwarebytes’ report which is largely based on data from the company’s Windows and Android anti-malware apps, helps provide some context as to how bad the ransomware problem has become.
According to the report, in January 2016, ransomware constituted 18% of all malware delivered by email or through exploits of existing software. By November 2016, it had climbed to 66%, which the report labels “an unprecedented domination of the threat landscape.”
The U.S. is the top target, while Russia, the home of many ransomware developers, is one of the least popular targets.
In a phone interview, Malwarebytes director of malware intelligence Adam Kujawa noted the pickiness exhibited by the two major families of ransomware, Cerber and Locky: “Both avoid any systems that appear to be coming from Russia or the surrounding countries.”
Old cons come back
But that’s not the depressing part of this report if you’ve been following the virus business for a while. That comes when you learn that Malwarebytes still sees a lot of malware getting on computers via in email attachments, many of which are Microsoft (MSFT) Office attachments with embedded macros whose code will attack your computer.
Those techniques date back to the days of dial-up internet, when Office was much more lenient about running macros in random documents and defending against them was harder.
And yet here they are again. As Kujawa put it: “Where are we, 2005?”
Today’s malware spam often comes personalized for particular users and tries to fool them into thinking that clicking a button in a Word document or Excel spreadsheet will unlock it for viewing, when in reality it will start a download of malicious code that can then take over their computers.
(You can read a detailed breakdown of one such attack in this December post from Sophos researcher Paul Ducklin.)
Other opponents
The Malwarebytes report also calls out a few other growing hazards online. One “ad fraud” malware, which can generate a decent amount of income for cybercriminals, proved nearly as popular as ransomware. Ad fraud malware commanders a victim’s computer to visit sites and click on ads placed by the authors of the malware attack or their business partners.
The report further nods to the rise in “botnet” software taking over computers — including “Internet of Things” devices like connected security cameras — and using them as part of distributed denial of service (DDoS) attacks. Unlike ransomware, however, the U.S. isn’t seeing the worst of this form of malware. According to Malwarebytes, 61.2% of all botnets are found in Asia, while about 15% are found in Europe.

Interestingly, the U.S. was the leading venue for Android malware, with 12.74% of all detections happening here. But if you stick to Google’s (GOOG) Play Store for downloading apps — the default in the U.S. — your odds of being the victim of an attack are exceedingly low.
Kujawa noted that Google does a good job of quickly yanking the occasional malware app that sneaks into its app market. He further added that Apple’s (AAPL) iOS, which can’t connect to alternative app sources, is even safer.
Not all software is created equal
While Malwarebytes’ report leaves it to the reader to figure out how to avoid being a victim of malware, Kujawa pointed out that many of these attacks can be thwarted by using current software.
“A lot of these exploit kits, the vulnerabilities they target, they’ve been patched for a long time,” he said. For example, he noted one common way criminals attack people’s computers is through an Adobe (ADBE) Flash flaw from 2012 — but his advice for that fast-fading media plug-in remains to “disable it entirely.”
(Follow Adobe’s instructions to uninstall Flash.)
The operating system you run matters, too. You may feel comfortable with Windows 7, but Kujawa called Windows 10 “a more secure operating system at the base level,” and other security researchers have come to the same conclusion.
The Mac remains relatively more secure, even after incidents like last year’s brief ransomware outbreak. Said Kujawa: “Every year, we say… this is the year when Mac malware is going to be huge, and it has yet to come to fruition.”
But more secure software doesn’t mean that malware authors will give up and get real jobs. They’ll just switch their attention to attacking our brains instead of our apps, trying various forms of social engineering to get us to pause our skepticism and click the wrong link just this one time, because it’s really important.
More from Rob:
Email Rob at rob@robpegoraro.com; follow him on Twitter at @robpegoraro.


