Hackers are getting better at tricking people into handing over passwords — here's what to look out for, according to experts

Paul Szoldra/Business Insider
Phishing scams in which hackers pose as trusted figures to trick people into handing over passwords are getting increasingly sophisticated.
Security experts describe an arms race between services that weed out scammers and attackers developing new tricks and workarounds.
Phishing is on the rise, and costing over $57 million from more than 114,000 victims in the US last year, according to a recent FBI report.
Hackers don't break in, they log in.
That mantra, often repeated by security experts, represents a rule of thumb: The vast majority of breaches are the result of stolen passwords, not high-tech hacking tools.
These break-ins are on the rise. Phishing scams — in which attackers pose as a trustworthy party to trick people into handing over personal details or account information — were the most common type of internet crime last year, according to a recent FBI report. People lost more than $57.8 million in 2019 as the result of phishing, according to the report, with over 114,000 victims targeted in the US.
And as phishing becomes more profitable, hackers are becoming increasingly sophisticated in the methods they use to steal passwords, according to Tanmay Ganacharya, a principal director in Microsoft's Security Research team.
"Most of the attackers have now moved to phishing because it's easy. If I can convince you to give me your credentials, it's done. There's nothing more that I need," Ganacharya told Business Insider.
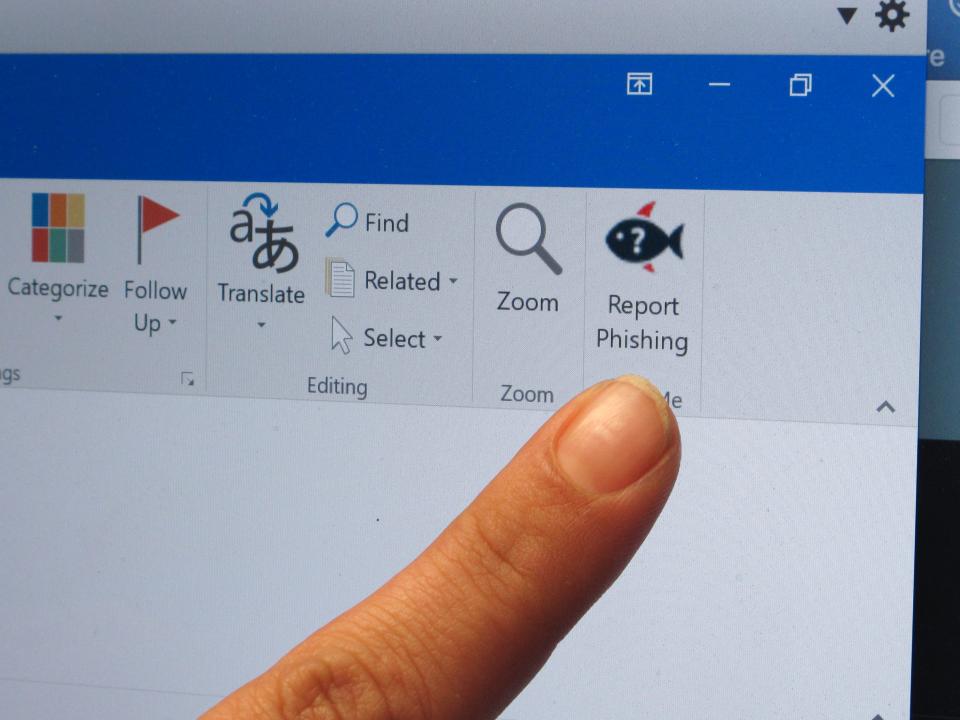
Ganacharya monitors phishing tactics in order to build machine-learning systems that root out scams for people using Microsoft services, including Windows, Outlook, and Azure, Microsoft's cloud computing service.
Microsoft has led a crackdown on phishing scams that impersonate its products — it seized a group of sites in July that targeted millions of people after pursuing a civil action against the scammers and getting permission from a judge to secretly seize their domains.
Ganacharya spoke to Business Insider about the trends in phishing that his team has observed. Many of the tactics aren't new, but he said attackers are constantly finding new ways to work around defenses like Microsoft's threat protection. Here's what he described.
Hackers will start by targeting low-level employees, then "moving laterally" to compromise executives' accounts.

Associated Press
Hackers will begin by sending low-level employees emails that look trustworthy, but might include links directing them to a scam website that asks them to input their username and password. Once they have access to that employee's account, they can use it to send trustworthy-seeming emails to others in the company.
"You might get into a network through someone, like a sales associate. But then through that you can laterally move by sending phishing emails to, let's say, the admin of that candidate," Ganacharya said. "And then once you're able to compromise the admin, you can actually leverage that company's domain and send emails to the larger cargo."
Similarly, scammers string together phishing attacks by compromising small, vulnerable businesses and leveraging their trust with larger business partners they work with.

Justin Sullivan/Getty Images
"Instead of the email coming from 'someone at gmail.com' or some random address, it actually comes from a business that they work with. In phishing it's all about gaining the trust of the email, the reader, so that they click on it. And if it is a credential thing that pops up, they just give their credentials," Ganacharya said.
The old-school tactic of "typosquatting" is also seeing a resurgence among hackers, according to Ganacharya.
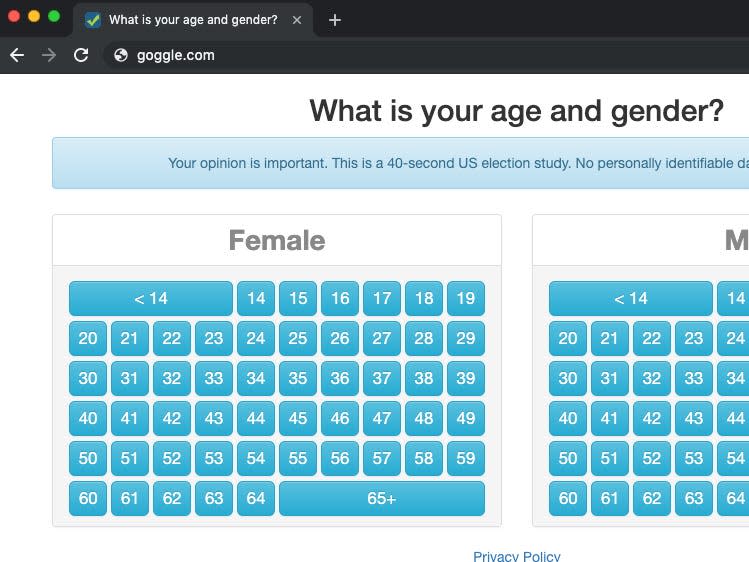
goggle.com
"Typosquatting is big again," Ganacharya said.
In this phishing scheme, also known as URL hijacking, attackers buy domains that are slight misspelling of popular websites, like goggle.com or yuube.com. The tactic was a mainstay of the early days of the internet, but has recently seen a resurgence.
"Spear phishers" put extensive effort into targeting a specific person, often creating multiple misleading pages to trick them.
AP/Kantele Franko
Hackers will sometimes create fake social media pages or personal blogs for the persona they're using to target someone, intentionally adding their targets' friends in an effort to seem more trustworthy.
Fake credential pages are becoming more sophisticated.

Trustwave
Hackers will regularly make fake sites that mimic the login screens of trusted services, like email accounts. Ganacharya's team has built machine-learning systems that detect subtle differences in the appearances of the sites and flag them as fraudulent, but he said hackers are constantly building workarounds.
"If the attacker created a similar looking page [to a legitimate login screen], but then they were not able to match a font here and there or something is moved by one pixel, the machine learning models can pick that up," Ganacharya said.
A cottage industry of phishing-as-a-service is booming as scams become increasingly profitable.

Sophisticated hackers are now willing to sell their services to specific organizations, individuals, or nation-state entities who want to steal information from someone.
Some phishing-as-a-service providers offer networks of bots that proliferate fake websites, while others sell phishing toolkits to clients, according to Ganacharya.
"If you have the funding, you can go buy a phish kit or sign up for phishing as a service and they will build everything for you, and you just have to hope your payoff comes out higher than what you were paying the phishing-as-a-service company," Ganacharya said.
Read the original article on Business Insider

