Beware, there’s a Gmail phishing scam going round and here’s what you need to know
While we’re pretty sure most people these days are pretty careful when it comes to the safety of their information and their emails, there’s a new Gmail phishing scam and it’s seriously concerning.
While we’ve only just got over the Netflix scam of a few days ago, it seems that users of Google’s popular email client are being targeted in fresh cyber attacks on the regular person.
Described as “highly effective,” researchers at WordFence, a tech company that makes security for the popular web platform WordPress, discovered the scam, and warned users of it in a blog post. Similarly, Satnam Narang, Senior Security Response Manager at Norton by Symantec, also told Refinery29 about how the scam works.
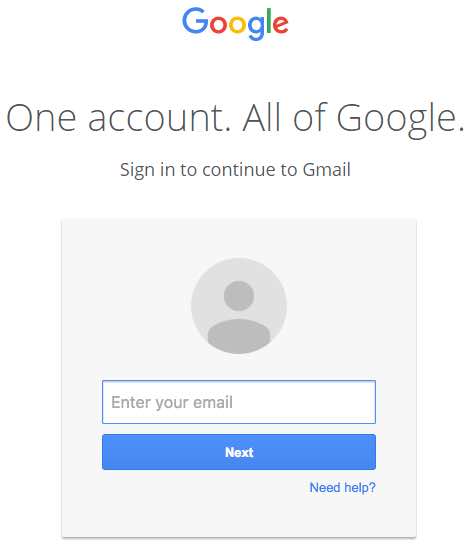
Essentially, you’ll see an email in your inbox from a friend who has already been hacked. That email will look like it contains an attachment of a pdf. Clicking on the “attachment” to provide a preview (as one does in Gmail), however, sends you to a new tab where you’re prompted to input your login details.
This is the closest I've ever come to falling for a Gmail phishing attack. If it hadn't been for my high-DPI screen making the image fuzzy… pic.twitter.com/MizEWYksBh
— Tom Scott (@tomscott) December 23, 2016
As WordFence point out, a cursory glance at the URL of the new tab *might* just deceive you into thinking that it’s actually your Google account (those paying attention, however, will notice that it’s proceeded by “data:text/html,”).
Similarly, the login page looks IDENTICAL to that of the usual Google login page.
However, once you put your details in your account is immediately compromised.
One user on Hacker News described the phishing scam in detail.
“The attackers log in to your account immediately once they get the credentials, and they use one of your actual attachments, along with one of your actual subject lines, and send it to people in your contact list,” they said. “For example, they went into one student’s account, pulled an attachment with an athletic team practice schedule, generated the screenshot, and then paired that with a subject line that was tangentially related, and emailed it to the other members of the athletic team.”
So, here’s what you need to be on the lookout for.
Satnam Narang told Refinery29 that “[t]he best way to identify this attack is to look at the address bar.”
“In this case, look for the words ‘data:/text/html’ at the beginning of the URL,” he continued. “If you see this, close the browser tab and alert your friend that their account has been compromised.”
It’s also recommended that you set up two-stage verification for your Gmail account. You can learn more about two-step verification here. It’s also recommended to boost your password strength, too, and if you’re using Google Chrome to check for the green lock symbol. Similarly, the URL shouldn’t be proceeded by anything except “http://”
In a statement, Google said that they were aware of the scam, and that they were working to “strengthen our defenses against it.”
“We help protect users from phishing attacks in a variety of ways, including: machine learning based detection of phishing messages, Safe Browsing warnings that notify users of dangerous links in emails and browsers, preventing suspicious account sign-ins, and more. Users can also activate two-step verification for additional account protection,” they said.
It’s important to note that while this scam is primarily focused on Gmail users, WordFence noted that users of other services should remain vigilant. Similarly, you should check and double check the URL bar and see if there are any discrepancies you’re noticing. Finally, check to see what it is that you’re actually clicking on.
Stay safe!